AML/KYC (anti-money laundering/customer due diligence) system and international financial sanctions procedures. Internal controls for the implementation of the AML law
The AML Law provides for a set of measures that help to deal with illegal actions related to money laundering and concealment of the true income of an individual or legal entity, as well as illegal sponsorship of terrorist groups. The law details how financial transactions are secured to avoid violating due diligence requirements, while also taking into account international sanctions that limit criminal activity. The legislation also provides for the existence of measures to detect transactions that may be considered suspicious. Non-standard financial transactions and transactions attract increased attention from regulatory authorities, and therefore are subject to increased scrutiny.
Analysis of basic concepts and notation
A company operating under the AML/KYC system must check its clients for the use of illegal means and ways of generating income, as well as the direction of assets to support illegal entities. In particular, we are talking about the money laundering procedure, which is the concealment of the true actions, goals, methods of obtaining or transferring property and rights to it. As well as money laundering, the receipt of income from fraudulent activities and other criminal activities is also defined. According to the AML law, money laundering is manifested in the following actions:
- providing financial support to participants in criminal activity;
- evasion of taxes, state duties and, in general, legal liability for making a profit;
- receipt, transfer, purchase, possession or use for one"s own purposes of funds or property obtained as a result of illegal activities;
- concealment or deliberate distortion of information about the source of profit;
- the acquisition of valuables and property with funds obtained in the course of illegal activities in the territory of other countries.
Also, money laundering is often associated with the financing of criminal groups, up to terrorist gangs, which pose a threat to the life and health of many people. The Criminal Code defines the process of sponsoring terrorists as illegal and brings to justice not only those who themselves were directly involved in transferring money to criminals or making profits, which are later directed to support groups, but also those who have certain information about the movement of financial flows, sponsored by terrorists. The AML law allows you to identify unreliable clients who were seen in dubious transactions or actions with money, impose sanctions on the activities of the client or the company he represents, and also bring him to criminal liability, if necessary and provided for by law.
Sanctions are a kind of enforcement measures that allow you to stop unwanted activities, prevent conflict, enhance security, as well as strengthen democratic foundations, maintain power and law, and protect human rights. If sanctions are imposed by international organizations - such as the EU, the UN or the government of the state at the international level, then the sanctions are called international.
The following concepts will also be mentioned in this guide:
- PEP is an English abbreviation that means politically exposed person. Technically, this is an individual who currently holds the position (or previously held it) of the head or member of a state organization, authority, including the government, parliament, ministry, legislative, judicial or executive branch of government, as well as international organizations, councils directors of a separate enterprise, etc.
- A local politically vulnerable person is an individual who holds an important position in the organization of a certain state, as well as local authorities that are involved in solving regional problems.
- A PEP family member is an individual who is a spouse or their equivalent of a PEP, as well as a child or parent, that is, who is in direct family relations with a PEP person.
- An approximate person of PEP - this may be an individual who represents the interests of PEP, is a co-owner of the enterprise, is in direct business relations with PEP.
In order to avoid confusion in the interpretation of the AML law, its main provisions and norms should be strictly adhered to.
Main provisions of the law
In accordance with the AML law, this manual must be communicated to all employees of the company and its customers. The guide is intended for purely internal use and uses information derived from the original text of the AML law and the International Sanctions Law.
All employees of the company are obliged to follow the requirements described below in order to prevent money laundering by clients, sponsorship of terrorist organizations, as well as other types of illegal activities related to obtaining illegal income. In addition, company employees should privately read the text of the law and its important additions, as well as the text of other legislative acts that are directly related to the limitation and prevention of money laundering.
The Board of Directors of the company undertakes to convey these instructions to each employee with the obligatory confirmation of reading and consent of the employees. At the same time, all employees undertake to follow the instructions and be responsible for complying with the requirements of the law in full accordance with the procedure provided for by the AML law.
Working with clients: identification procedure
Each employee of the company who is familiar with the work procedure, in accordance with the law, must use certain rules for interacting with the client. They must work every time an employee of the company and the client enter into a business relationship. At the same time, it is important to note that business relations of employees with representatives of clients who have all the necessary powers are not provided for by the company.
Identification of the client as an individual is carried out as follows.
- The first condition for successful identification is the provision of a document that can confirm the identity of the system user. For this purpose, you can use both a passport and a residence permit, international passport, driver"s license or a copy of any of these documents.
- The employee records and saves the data of each client - full name, passport data, identification code, date of birth, place of registration and residence, as well as data on the state organization that issued the document used to identify the client. In addition to these data, a company employee records whether the client belongs to the PEP status or family members / PEP partners. It is also important to save contact information for communication with the client - e-mail and mobile phone number.
- In addition to a document that can officially confirm the identity of the client - passport, international passport, driver"s license, residence permit, etc., it is necessary to provide a document that confirms the address of residence of the system user. As such, an invoice for payment of utilities or banking services can be used, the validity of the document is no more than 3 months.
If the client of the company positions itself as a legal entity, identification takes place according to a slightly different scheme. Firstly, an extract from the register is required, issued no earlier than 3 months before submission to the company employee. It is important that the extract be notarized and apostilled, if possible. An employee of the company records the following data for each legal entity - client:
- name of company;
- date of registration of the legal entity and the number assigned during registration;
- the legal address of the organization and the actual location of the office;
- information about persons who may represent a legal entity, as well as about the owners of the organization and shareholders.
It is mandatory to collect contact information for communication with the client - phone number and e-mail. If there are individuals in the legal entity, it is necessary to collect separately for each the data package for identifying individuals, described above.
Procedure for assessing risks and determining control measures
When entering into business relations with any client, the company, in accordance with the AML law, undertakes to analyze its reliability and risk level - to assess the likelihood of sponsoring terrorist organizations and money laundering by a specific person based on the information provided by him. To check the client"s trustworthiness, a set of measures for conducting a legal check is determined.
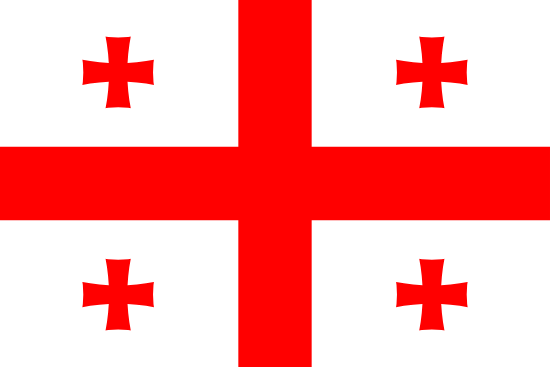
Three main risk indicators are used for assessment – operational, client and geographical. It is these parameters that are taken into account in the first place when assessing risks. Geographical is determined by the client"s involvement in relations with states and territories that were previously subject to international sanctions, as well as with those countries that do not have an adequate level of verification and prevention of financial complicity in terrorism and money laundering. Clients who are located or have ties to states with a high level of corrupt activity, or who are known to support terrorist groups, are also at geographic risk.
With regard to client risk, this indicator refers primarily to PEPs, persons close to them and members of their families. That is why the company"s employees at the stage of registration are required to find out if the client belongs to this category. Further, according to the law, persons under international sanctions should be classified as clients with increased client risk. Even before the client enters into business relations with the company"s employees, they have the opportunity to check it, having data on the sanctions lists.
Also, a high client risk is a person who was previously seen in conducting illegal activities, carrying out illegal financial transactions, money laundering or aiding terrorist organizations.
The last indicator - operational risk - is considered high and requires a thorough check of the client if:
- payment for the transaction is transferred to an outsider who does not appear in its execution;
- when concluding a transaction, the client is asked to hide the list of its participants;
- when concluding a transaction, its purpose is not clearly outlined;
- when working with digital assets, they are received from different accounts;
- the amounts used for transactions or credited to the client"s account are not typical for this user (usually they significantly exceed the standard values);
- each financial transaction is carried out using different cryptocurrencies.
In each of the described situations, there is a high risk that the client is involved in money laundering and may be associated with the financing of criminal activities, which is why the company clearly defines the categories of clients who cannot receive the company"s services:
- clients residing in or with links to high-risk countries;
- clients included in the sanctions lists of international organizations;
- politically vulnerable persons, their representatives and family members;
- individuals who have previously been prosecuted for financial aiding terrorism and money laundering.
If a client does not belong to any of the above categories, but for one reason or another, the company considers its activity suspicious, it has every right to authorize a special due diligence in an enhanced mode. Risks associated with information technology and the possibility of their control
Depending on the information technologies used, this section covers the following IT risks:
- Data leakage due to the use of low-quality software or human error.
- Providing false information by clients - forgery of identity documents, etc.
- The use of malware, the replacement of original programs with hacker programs with embedded malicious code, the implementation of cyber attacks.
- Problems that may arise in the operation of the information system
In order to prevent the leakage of personal data of customers and other information that is vital for the correct functioning of the company, its employees are obliged to:
- work exclusively with internal servers of private organizations with limited liability;
- use only licensed software that is permitted for use and approved by the Board of Directors (it is important to regularly update software versions and check for technical failures);
- use only the equipment and software of the company, it is strictly forbidden to use your own technical means in your work.
To prevent the possibility of providing false information, in particular, client personal data, it is necessary to use special means of confirming information. Alternatively, you can communicate with customers via video or confirm the data at a real meeting between an employee and a client. If it is suspected that the client is providing false information or withholding important information, documentary evidence of these data should be requested.
To reduce the risk of third-party penetration into the system through a cyber attack, the following actions are taken:
- regular checking of the system to detect suspicious activity of its individual sectors;
- constant testing of the system security service and the development of new methods of protection;
- use of constantly updated software to detect viruses and other malicious programs.
To reduce the risks that are associated with the operation of the system, separate servers and systems are used to store backup copies of information that allow you to restore information lost as a result of a failure. The company also organizes the safety infrastructure of the system. The company guarantees the use of a certified information system (according to PCI/DSS).
Additionally, periodically, but not less than once a year, specialized training of company employees in terms of information security and a control check of the system security level are conducted.
Due Diligence Measures
When working with clients and participating in business relationships within the framework of the company"s work, special attention should be paid to actions, information or other factors that may directly or indirectly indicate involvement in money laundering or the use of funds to sponsor criminal, including terrorist activities. Often this can be indicated by a deal of a non -standard plan, which does not have a reasonable goal and is quite difficult to implement. To verify such transactions and the persons participating in them, the following due diligence measures are used:
- careful confirmation of the identity of the participant in the transaction, including using not only documents and their copies, but also video communications;
- the requirement to provide detailed information about the client"s activities, his connections and the purpose of the suspicious transaction;
- regular verification of the client: his personal data, transactions and other information that can confirm the purity of the client"s intentions.
Constant monitoring of identification data is also actively used in the work, regular requests are sent to the client to update data and documents. Additionally, the company may conduct an investigation in order to identify the source of funds that are used in the completion of a particular transaction.
Due diligence usually relies on documented facts based on original documents provided by the client. Copies in this case cannot be sufficient evidence, except for copies certified by a notary or a lawyer, if for some reason the original documents cannot be provided. When checking, you can also take into account the data of commercial registers and credit institutions of states that put forward similar requirements for AML / KYC. All these actions must be carried out even before the start of cooperation with the client or before the completion of a certain transaction.
If the risk is low, then the verification can be carried out routinely while working with the client. In any case, all documents requiring confirmation by the client"s signature must be signed by him.
Extended due diligence and features of its implementation
Due diligence is carried out in an expanded form in several situations.
- If the customer information is validated, but the data is not from the specified source, which does not match the customer"s specified physical location.
- If during identification, registration or verification, employees of the company have suspicions about the veracity of the data provided, including the authenticity of the documentation.
- If it is not possible to accurately confirm the identity of the client if necessary.
- If the situation has a high risk of money laundering or sponsoring terrorist operations/organizations.
In any of the above situations, an employee of the company has the right and obligation to resort to extended verification measures and use at least one of them. These measures include.
- Confirmation of the client"s identity with the help of additional reliable sources, for example, in independent organizations in which the identification of an individual was carried out in his presence. These can be credit organizations, state registers and other institutions that contain true information about the client.
- Using the method of electronic delivery of documents for the purpose of verifying their authenticity and certification by a lawyer or notary.
- Work with a credit institution that opened an account in the name of the client and transfer the payment to this account. It is important that the lending institution is subject to similar AML/KYC requirements.
All these measures are within the competence of the company"s employees and can be applied, if necessary, to any of the clients in case of problems with identification and doubts about the legality of transactions.
Procedure for identifying a politically vulnerable person
When filling out the questionnaire, the client is obliged to indicate a number of data that are required by law and are used to further identify the client and verify information. In particular, the user of the system must indicate that he is a PEP, either a member of the PEP family, or a trustee or partner of the PEP. In the case when the client is a relative of a PEP or its representative, he must also indicate the details of this PEP. The information provided is subject to mandatory verification, which is carried out by the company"s employees using reliable public sources.
The procedure for identifying a person who was or is currently on the sanctions list
When establishing a business relationship, the client must fill out a questionnaire in which he is obliged to provide all the necessary information for conducting the appropriate verification. After that, the employee, using official sources, will check whether the client is now under international sanctions, and whether he really provided real information when identifying.
A number of signs indicating money laundering
This section describes in detail the circumstances and signs that may directly or indirectly indicate the client"s involvement in money laundering and, at a minimum, should arouse suspicion among a company employee. Based on these signs, a deeper check of the face can be initiated.
Option one - a person in itself does not inspire confidence. Signs that indicate the likelihood of money laundering:
- the status, appearance and behavioral characteristics of the client do not correspond to the content of the transaction, the person behaves suspiciously;
- the client does not sign documents on his own, referring to the need for outside assistance;
- the client was previously suspected or accused of criminal activity and fraud with finances;
- the client is not able to clearly explain the essence of the transaction and its purpose;
- the client requests too high a rate, which is unreasonable in this situation;
- the client conducts a non-standard transaction using cash;
- the client conducts transactions with digital currency (one-time large in volume or frequent small ones), while such activity does not correspond to the type of activity of the client;
- the client transfers funds to another name, or to his accounts in other countries, including those with a high geographic risk;
- the client refuses to provide information regarding the purpose of the transaction;
- the amounts involved in transactions are unusually large and do not correspond to the activities of the client;
- the client cannot be identified, or he refuses to provide the information necessary for identification;
- the transaction looks or is fictitious;
- the settlement is supposed to be carried out mainly in cash in the long term;
- the client behaves suspiciously, presumably acting in the interests of others;
- the client plans to conduct large transactions in cash (more than 10 thousand euros), or has repeatedly paid bills in such large amounts;
It is also worth paying attention if the payment is made through a bank located in a tax-free territory.
Refusal to complete a transaction
The company has the right to refuse the client to complete a transaction or conclude a contract if:
- the client has not reached the age of majority (18 years according to the current legislation);
- instead of the client, his authorized representatives try to make a transaction (if the client is an individual);
- the client refuses to provide the data and documentation necessary to confirm his identity or gives deliberately false information that does not correspond to reality;
- the client is suspected of carrying out provocative actions;
- during the verification, according to the client’s data, information was obtained confirming the laundering of funds or sponsorship of terrorist organizations;
- the client has been included in international sanctions lists;
- the client is a PEP, its partner or a family member of a politically exposed person;
- the client has previously been seen in money laundering or financial complicity in terrorism;
- the client is a citizen of a country with a high geographic risk;
For each client and the information provided by him, a check is carried out to identify users included in the above list.
Collection of information, its registration and storage
As soon as the client enters into a transaction, the employee is obliged to collect and record all information regarding the participants in the transaction and the parameters of its implementation. In particular, the following information is subject to registration:
- customer data, according to the identification procedure;
- when the transaction takes place;
- the content of the transaction;
- information about the refusal to conduct the transaction, if any (at the initiative of the company or the client);
- data on the completion of cooperation, including due to the impossibility of conducting a legal audit;
- data on the service of the exchanger and information on the current exchange rate of the currencies used in the transaction at the time of its completion, as well as on the amount;
- if the client has opened an account in cryptocurrency, then, among other things, the type of currency, account number and name of the currency are indicated.
All documentation on a specific transaction is subject to storage in the company for 5 years. This list includes the following documents:
- personal data of the client used for identification;
- letters, notifications and other correspondence that was sent or received by the client;
- information collected by the company"s employees in the course of checking the client, monitoring his activities and relationships with the company;
- confirmed data on suspicious transactions;
- transaction documentation.
When collecting, classifying and storing documentation, company employees are required to act in accordance with personal data protection methods, and also use the information received solely for the purpose of combating money laundering and financial aiding to terrorist organizations.
The procedure for notifying the financial monitoring service if necessary
Verification of client data may reveal credible information about participation in money laundering or involvement in the financing of terrorist operations. In this case, the employee who identifies the suspicion or discovers undeniable facts pointing to it must report to the appropriate inspector of the company that deals with anti-money laundering (MLRO). In this case, the client is not informed about the transfer of his information to the MLRO. When submitting a notification, all necessary documents about the transaction, the client"s personal data used to identify the client and other documents, if any, confirm the employee"s suspicions, are attached.
Implementation of internal control and training of specialists
The Company"s Board of Directors plays a leading role in complying with the requirements of the International Sanctions Act and the AML Act. It is he who selects and trains employees who conduct risk assessments and check clients for involvement in money laundering. The management of the company is also responsible for those employees who enter into direct business relations with customers and conduct transactions with them. The Board of Directors ensures high-quality training of employees and their training in accordance with the requirements of the law at least once a year.